DocuSign user information found through Google search
As the world’s largest electronic signature platform, DocuSign says that they have over 6 million unique signers processing millions of transactions per year and that they are “trusted by more people, more companies, more times than any other electronic signature provider in the world.”
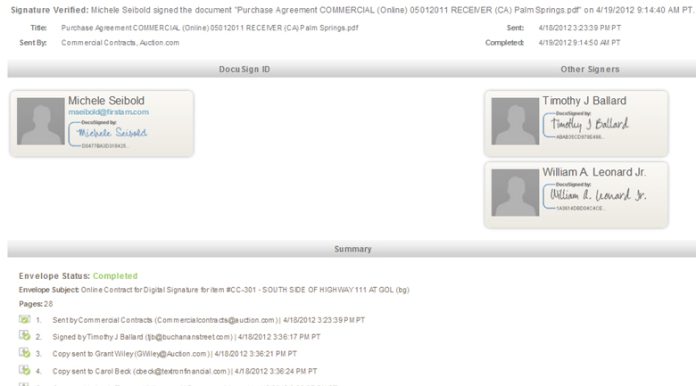
In just one search query in particular, we uncovered 4,450 URLs filled with DocuSign customer names, emails, document names, and GPS coordinates of where documents were signed. These details are found on websites with URL structures appearing like the one below (which is not a functional link that takes you to a signed document, just an example):
[ba-quote]https://www.docusign.net/Member/DocuSignTrust.aspx[/ba-quote]
DocuSign tells AGBeat that while the documents appear to be hosted on their secure https servers, “They are not. Anything that is found via Google search is not from DocuSign’s secure site, but rather the publicly accessible and searchable locations where customers have saved their personal copies of signed documents. In order to access documents, data, or transactions on the DocuSign Global Network, you must have the login credentials and password.”
We do not yet know the full scope of the number of transaction details that can be seen via Google, but we can see that they go as far back as at least January in our preliminary investigation. We have not made public how to discover these documents due to security risks, but suffice it to say that we can see the private emails, signatures, times, dates, locations, and document names (hypothetically speaking, we can see “Listing on 201 Main Street” or “Employment Contract – $58k/yr” as document names).
On the heels of a hacker leaking LinkedIn and eHarmony passwords, the leaking of personal information and potential details of legal documents that are meant to be private, is a major problem for several industries and feeds the hysteria behind cloud based storage and digital data sharing.
The company tells AG that “While DocuSign encourages customers to save their signed documents on the secure DocuSign Global Network, we are also required by law to offer customers the ability to download and retain their own personal copies,” adding that “it appears that a very small number of DocuSign users have saved their own personal copies of their signed documents to publicly accessible and searchable locations outside of the secure DocuSign Global Network. In the event that customers need to save signed documents in a location outside of DocuSign, we encourage that they ensure the location meets the security requirements of all signing parties.”
DocuSign asserts their “commitment to security” as outlined on their website. DocuSign is the official and exclusive provider of electronic signature for the National Association of Realtors’ nearly one million members, under the REALTOR Benefits Program, and is used by many industries, including users like American Airlines, LinkedIn, Sony, and Yamaha.
After publication, all links formerly discovered through a Google search appear to no longer be clickable, but can still be viewed through the Google cache, as seen in the before and after below.