
High school prom policy could be problematic
Have you seen pictures of what some kids are wearing to prom these days? It’s like a contest to see who can dress the most inappropriately, and a huge portion of attendees are hellbent on winning. Schools nationwide are struggling with a number of issues for this off-site event to keep kids appropriate and safe – it’s a huge challenge nationally.
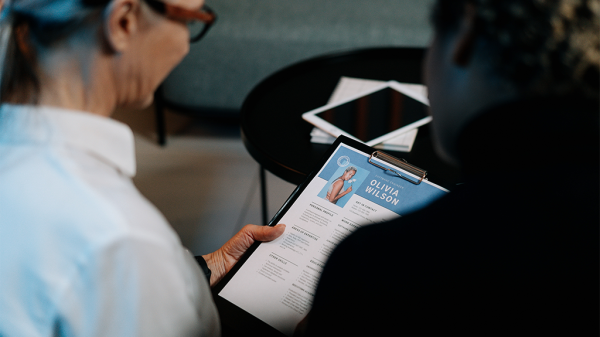
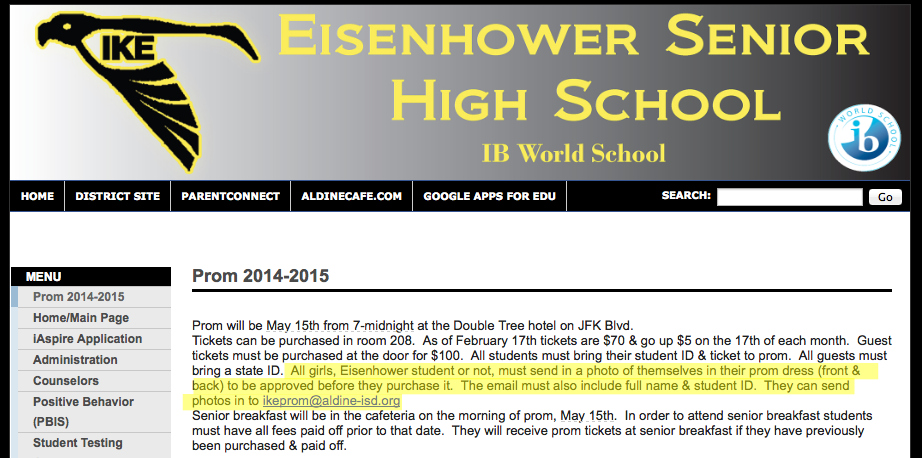
While none of this is new (I remember some pretty revealing prom outfits in the late 90s when I was in high school), technology has been injected into the equation as one high school in Texas is requiring female students to email photos of themselves in their prom dresses for approval (regardless of their age). Parents say no notice was sent out, this just appeared on the Eisenhower Senior High School website:
“All girls, Eisenhower student or not, must send in a photo of themselves in their prom dress (front & back) to be approved before they purchase it. The email must also include full name & student ID. They can send photos in to ikeprom@aldine-isd.org.”
Why this policy?
We have reached out to the school for clarification, but some have told us that their assumption is to insure appropriateness.
Other schools in the past have enforced dress codes, turning girls away for low cut dresses or strapless dresses, and banning certain dance moves and even music degrading to women. Some schools have forbidden girls from wearing tuxedoes and boys from wearing dresses or even kilts.
This policy, however, introduces new questions about why the school is taking this stance:
- Are strapless dresses allowed? Can cleavage be shown? What about middriffs? Plain clothes? Hats? Combat boots or black jackets? Costumes or capes?
- Why not require male students to submit pictures of their outfits prior to the event? What if suits are overly baggy and underwear can be seen? What if it’s a batman costume?
- Are girls required to wear a dress? Are suits for girls be banned?
- Are there color restrictions to avoid gang warfare and keep kids safe?
- What is the purse policy? May someone bring a bag? Will purses or bags be subject to search? Will photos of accessories be required for approval as well?
As a parent of a daughter who just went to her second prom, the policy complicates the shopping process – if her school asked us to submit a photo and wait some amount of time, the dress may no longer be on hold and our daughter would be crushed at a lost opportunity. Also, we have forbidden her from taking photos of herself inside of a dressing room, which is most likely what these girls at Eisenhower will be doing – does someone at the school have a thing for feet or underage cleavage? As a parent, this email process would have me panicked.
![]()
There may be a good reason, but there could be serious legal implications
There is probably a good reason for the district’s policy, but the ACLU is just thirsting for another school to ban anything perceived as discriminatory against students’ gender identity.
That aside, we are focused on some logistic and tech questions for the school:
- Who has access to the photos of underage girls (and only girls)?
- Are they obtaining parent permission prior to transmitting personal photos of a minor (that could potentially be explicit in nature)? What child pornography laws have been considered by the district regarding soliciting images of minors?
- What is the purging process for these images? What servers or computers (or staff phones) will these images be on, and do parents have the ability to request their removal?
- What are students (and parents) consenting to when submitting images – any reuse? Will they post the rejected images on Instagram? Will they print acceptable photos in the halls or post them online?
- After submitting the photos, how long until the approval or rejection is given to the student? What is the school’s policy for adults communicating with minors?
- E-commerce is at an all-time high, so what of girls buying their dresses online?
- Will the original images submitted be cross referenced at the door to insure the girl is wearing the dress approved? What technology will be used to make this happen, and if it is a third party application, do they allow transmission of images of minors?
THE SOLUTION
Like every other school in history, there are dress codes and behavior rules students must follow at prom, lest they be removed (or not allowed in). The solution is to make the rules clear in advance and refuse admittance should those rules not be met. Introducing transmission of images of minors into the mix makes the district and the students vulnerable and is unnecessary.
There are bigger fish to fry. Schools are battling with students inviting adults to prom, like celebrities (from football players to porn stars), alumni, or college boyfriend/girlfriends without background checks… in a room full of children. Schools are taking positions on whether or not singles can go to prom or if they’re required a date, and whether gay couples can take a same-sex date. Further, schools are struggling with how to keep kids safe after prom, reduce drug use and drunk driving, date rape, and an assortment of other issues.
Schools need to set policies, enforce them, and deal with the fallout – not introduce technology into the mix… it could be caustic.
#EisenhowerProm
Lani is the COO and News Director at The American Genius, has co-authored a book, co-founded BASHH, Austin Digital Jobs, Remote Digital Jobs, and is a seasoned business writer and editorialist with a penchant for the irreverent.

































Pingback: Can High Schools Require Official Approval for Prom Dresses? | Internet Tax Lawyers