I’m not a lawyer, and I don’t play one on AG.
That said, while at GE I was pummeled with information security policies. Non compliance was not an option and even the tiniest of infraction, even assumed, was taken seriously. If, for example, during the nightly after-hours security inspection, a Post it was on a desk (or under a keyboard, mouse pad, phone, etc.) or in the trash with something resembling a password, it was reported, escalated and the offender counseled. No matter that there was no indication what the alleged password may be to – information security was a top priority. All documents were to be locked up or shredded before leaving for the day.
I appreciated that. As a victim of identity theft years ago I have experienced the pain and hassle of clearing it up. Now, with current economic woes, I think we will see instances of identity theft escalate. What better place to shop for a top notch identity than among home buyers.
Are you protecting your client’s identity?
You’re probably aware of the Gramm-Leach-Bliley Act (GLB) formally known as the Financial Modernization Act of 1999. I’ve read numerous opinions on how exactly it applies to Realtors® and agents, and I’m not an expert in that area. That said, here are some basic provisions regarding protecting a customers’ non-public information in a GLB compliant manner.
In a nutshell GLB is aimed at financial institutions and is enforced by eight separate federal agencies and the states. GLB provides for a fairly broad interpretation of the phrase “financial institution” and not only affects banks, insurance companies, and security firms, but also brokers, lenders, tax preparers, and real estate settlement companies, among others.
A few things to know:
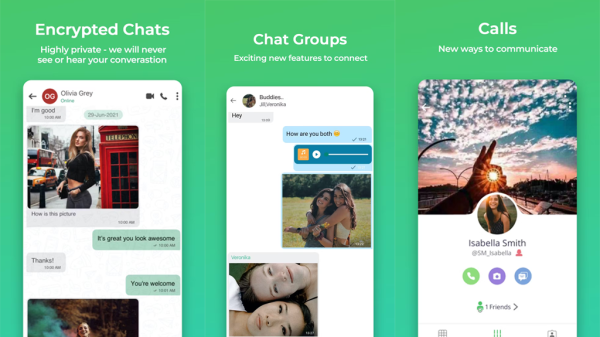
- Data should be encrypted in storage and in transit.
- Both non-public & public information must be protected.
- Compliance is not limited to IT.
- Annual privacy policy information should include more than a Web page.
- Businesses must keep tabs on third-party providers.
- Data you don’t need should be destroyed.
Financial institutions are responsible for:
- Insuring the security and confidentiality of customer records and information.
- Protecting against any anticipated threats or hazards to the security or integrity of all records.
- Protect all information against unauthorized access to or use of such records or information which could result in substantial harm or inconvenience to any customer.
The following is considered personal information (in paper or electronic form – list non-exhaustive):
- Names
- Addresses
- Phone numbers
- Bank and credit card account numbers
- Income and credit histories
- Social Security Numbers
- Phone numbers
- Other financial and tax information
Data in motion
Data should be encrypted in storage and in transit. “In transit” means email and instant messaging. Both are easy ways for confidential information to leave the organization in an unsecured manner. If a customer experiences identity theft, you could be at risk if you (or anyone involved in the transaction on your behalf) are sending non-public personal information in an email, or as an attachment to an email.
Penalties for Non-Compliance
Violation of GLBA may result in a civil action brought by the U.S. Attorney General. The penalties include those for the company of up to $100,000 for each violation. In addition, “the officers and directors of the financial institution shall be subject to, and shall be personally liable for, a civil penalty of not more than $10,000 for each such violation”. Criminal penalties may include up to 5 years in prison.
How will they know?
If a customer experiences or suspects identity theft and retains a lawyer in to find the responsible party, the lawyer will typically hire forensic computer experts who comb through huge volumes of e-mails looking for a smoking gun, in the form of certain words and phrases. They can find it, even if you’ve deleted it.
Consult an expert
Take a walk around your office after most people have left. If you see files on desks, that’s a sign a check-up is in order. An information security consultant or expert should be able to review your processes and systems to ensure information security.
What are you doing to ensure your clients’ identities remain safe under your watch?
Brandie is an unapologetically candid marketing professional who was recently mentioned on BusinessWeek as a Top Young Female Entrepreneur. She recently co-founded consulting firm MarketingTBD. She's held senior level positions with GE and Fidelity, as well as with entrepreneurial start-ups. Raised by a real estate Broker, Brandie is passionate about real estate and is an avid investor. Follow her on Twitter.



































Matthew Hardy
June 4, 2009 at 12:24 pm
Excellent post. I used to write medical software for universities, hospitals and corporations and when HIPAA came along things needed to be screwed down pretty tightly.
In my earlier years in the real estate software business, I predicted that one day sellers would slide an NDA (non-disclosure agreement) across the table during a listing appointment requiring that the agent not store important private information on a website. In one of my recent talks before a group of agents, a woman said exactly that scenario happened to her recently. Consumers are indeed getting more attuned to data privacy issues.
Joe Loomer
June 5, 2009 at 12:23 pm
Awesome Brandie. In my past life as a Navy Cryptologist, procedures for handling and storage of any classified materials – or the ubiquitous “Official Use Only” stuff – was a constantly monitored, drilled, and re-drilled affair. There where instructions, regulations, directives, posted orders, posters, you name it. “Loose Lips Sink Ships” and all that. The rationale had nothing and everything to do with identity protection, but the premise is the same.
Thanks for this awesome refresher for those of us who need to take another look around the office and our other data storage mechanisms.
Navy Chief, Navy Pride
Ken Montville - The MD Suburbs of DC
June 5, 2009 at 12:34 pm
I suspect that if you mention a particular color is purple and it is later determined to be lavender, fuchsia or mauve you can be sued. Some of the lengths we are required to go to in order to facilitate the smooth and orderly transfer of real estate from seller to buyer are mind boggling.
I’m not going to invest in super secret double dog dare Get Smart Cone of Silence technology with a bullet proof titanium briefcase hand cuffed to my wrist while being accompanied by two burly escorts just to get a contract and all the appropriate addenda from point A to point B.
I’ve just now reached the point where I can send offers and documentation to an individual agent (vs the office fax for the world to see) and receive documents into my individual e-mail (vs getting lost at the office fax machine).
Yeah. It’s important to be careful and respectful or people’s information. The scenario you lay out is just plain crazy. The world has gone nuts.
Brandie Young
June 5, 2009 at 5:18 pm
Hi Matthew – thanks for your comment. That’s interesting … bringing an NDA to the table. It’s good consumers are aware!
Hey Joe – good to hear from you! Yep, same premise …
Hi Ken – yep, we do live in a litigious society. I hear you on “over-buying” technology – but that’s not at all necessary. Secure servers for data storage should be a part of your business practice, as should proper document disposal (shredding). FYI, sending docs over email …. EEEEEK (as Ginny Cain would say). That’s not secure – and you could face some steep fines if it’s determined that as a result of such an email a person’s confidential info was compromised. The fax is (in transmission, the part about “all the office to see” is another animal). I don’t know … I’d rather work with the guys that go over the top to protect my identity that worry about it.
Matthew Hardy
June 5, 2009 at 6:56 pm
@ Brandie “sending docs over email”
(…trying my best to stay within good guidelines…)
Documents from our software REST can be output as PDF and password protected. A password can be required to open the PDF and/or to print, edit or copy text and images.
Atlanta Real Estate
October 2, 2009 at 3:54 pm
Brandi:
Going back and reading interesting posts here. Very interesting post and very true information.
When I was selling EDA Software, a ot of it was into Defense Contractors. Same level of security with those guys. Just getting in and out of the building was a major chore.
Anyway, good post,
Rob in Atlanta