Internet brought to life
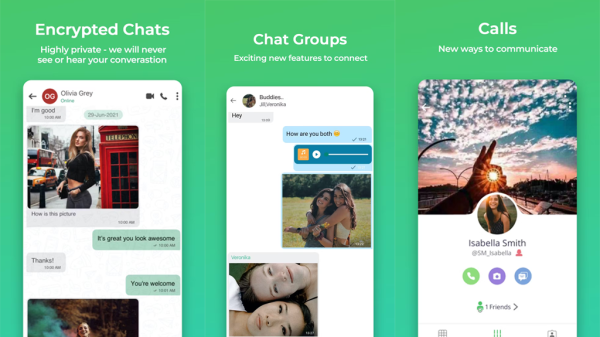
There are tons of startup tech companies with innovative products that are ready to solve problems and/or add a little whimsy to life for as many people as possible. Unfortunately for the problem-riddled world, many of these startups only exist on the internet, and don’t have the resources for brick and mortar stores. Most tech products are really best experienced in person, not in a video online.
![]()
An up and coming software-driven retailer is out to disrupt that disconnect between awesome products and the people who want to try and buy them. b8ta is a “retail destination” that features popular tech products, and they’ve announced that a new store will open in Austin’s Domain NORTHSIDE on Saturday, May 20.
b8ta
b8ta has adopted a retail-as-service model. That means that makers of awesome products can lease space in the storefront, and keep all the proceeds from any sales made in store. The retailer is also powered by software, which tracks the highest performing products and cycles products in and out on a month to month basis.
This is super cool both for makers looking for a chance to prove themselves, and for consumers looking for new products and experiences each month.
Designed by international architecture firm Gensler, the Austin location will feature over 3,000 square feet and more than 100 cutting edge products, including Soundwall, a flat panel speaker that can also serve as décor, and a Bluetooth-powered Neo Smartpen that captures data in the cloud as you write.
Numero quatro
This marks the fourth location for b8ta, which opened their first location in Palo Alto in 2015, followed by retail spaces in Seattle, Santa Monica, and now Austin. Located in a trendy new shopping district, the Austin store marks b8ta’s first departure from the West Coast, and will be its largest store to date.
The newest location will also feature a live performance area, and a space dedicated to emerging categories such as connected kitchens, like the June Intelligent Oven.
The Austin store will feature a range of popular consumer tech products, including the connected home robot by OhmniLabs, Soundwall, a flat panel speaker that doubles as art and a bluetooth Neo Smartpen that writes like a regular pen but captures information in the cloud.
where tech and real life meet
b8ta CEO and co-founder Vibhu Norby says the goal of the innovative retailer is to offer technology makers a cost-effective path to connecting with the public in real life. “The high tech products that we bring in are made by both engineers and artisans, and those makers are creating our new software-driven and networked culture. You couldn’t pick a better city than Austin for b8ta to open, the perfect melting pot of technology, arts, and culture.”
“b8ta empowers the entrepreneurs creating today’s most innovative products by making retail accessible to them—not just to the big companies that can traditionally afford a retail presence,” Vibhu said.
“At the same time, customers can expect to discover a variety of technology products they likely haven’t seen before, with inventory that changes monthly and a chance to touch, play, and learn about the latest innovations just coming onto the market.”
Real life experience
Ultimately, b8ta’s goal is to get cutting edge products into physical stores, and to facilitate real experiences for customers. Since their launch in 2015, b8ta has trained employees (“b8ta testers”) which have engaged with over 5.3 million shoppers, and led over 27,000 demos.
The retail-as-service model could be the saving grace of the struggling brick and mortar retail industry. Providing a real hands-on experience, and constantly evolving merchandise with a human element (here are the makers, here are their stories) gives customers something they just can’t get online
#b8ta
Staff Writer, Natalie Bradford earned her B.A. in English from Cornell University and spends a lot of time convincing herself not to bake MORE brownies. She enjoys cats, cocktails, and good films - preferably together. She is currently working on a collection of short stories.